Motivation
With SBOMs, we can do the following things:
- Using a Vulnerability Scanner to find potential vulnerabilities
- Determine whether a vulnerability we’ve discovered actually presents a risk to our device.
These two things are different, sometimes we can scan a lot of vulnerabilities, but it also often happens that a vulnerability is not exploitable under a particular configuration, like physical access is required, which means the vulnerability doesn’t pose a serious risk.
So, with SBOMs and potential Vulnerabilities, there is a priority list.
So, VEX, Vulnerability Exploitability eXchange, is used to help us understand what kind of level of risk a vulnerability may pose to the medical device.
Vulnerability Exploitability eXchange (VEX)
VEX is like a further extension of SBOM, based on the contextual information from SBOM, VEX can provide exploitability information for the vulnerabilities.
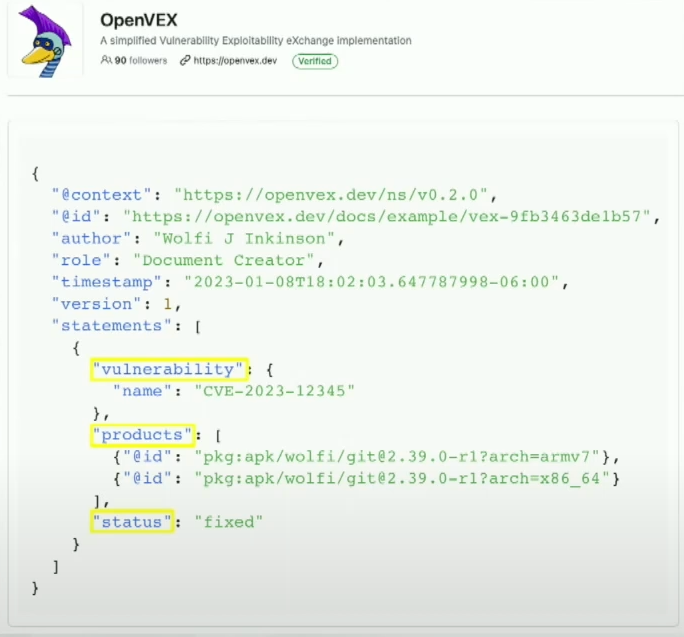
Composition of VEX:
- Vulnerability Information: CVE ID, CVSS Score, etc.
- Product Information (Context):
- Status (Statement): Whether the vulnerability is exploitable in the context of the product, and the reason for that status.
- Options: Exploitable, Not Exploitable, Unknown
Who has the responsibility to generate VEX? Where to find VEX?
- VEX is used to shrink the scope of vulnerabilities, to make the downstream users (like HCPs) to focus on the vulnerabilities that are really exploitable, so the responsibility of generating VEX should be on the upstream side, which is the MDMs (Medical Device Manufacturers).
- So basically, upstream vendors based on the product context and original vulnerability information, they can make statements about the exploitability of the vulnerabilities.
- Then downstream users can use the VEX information to prioritize their patching or mitigation process, to focus on the vulnerabilities that are really exploitable and pose a risk to the device.
Since VEX is just a concept, there are different implementations available for this concept.
VEX and SBOM
SBOM is used to track software supply chain components and contextual information associated with them.
VEX is used to describe the vulnerabilities.
VEX can be integrated into an SBOM to add information about vulnerabilities during scanning.
Resources
Todo
- [ ] https://www.aquasec.com/cloud-native-academy/vulnerability-management/vulnerability-exploitability-exchange/
- [ ] https://www.aquasec.com/cloud-native-academy/vulnerability-management/vulnerability-scanner/
- [ ] https://www.aquasec.com/cloud-native-academy/vulnerability-management/vulnerability-scanning-process/